AI-POWERED | CYBERSECURITY
RISK & COMPLIANCE AUTOMATION
From Months to Weeks
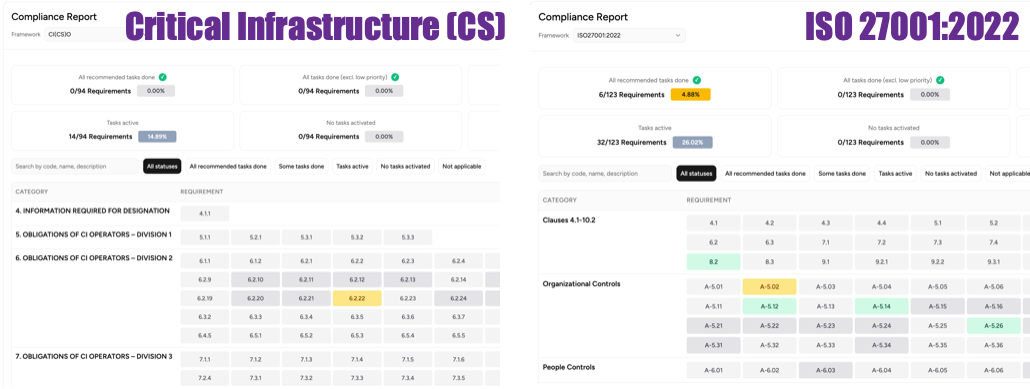
RISK AUTOMATION
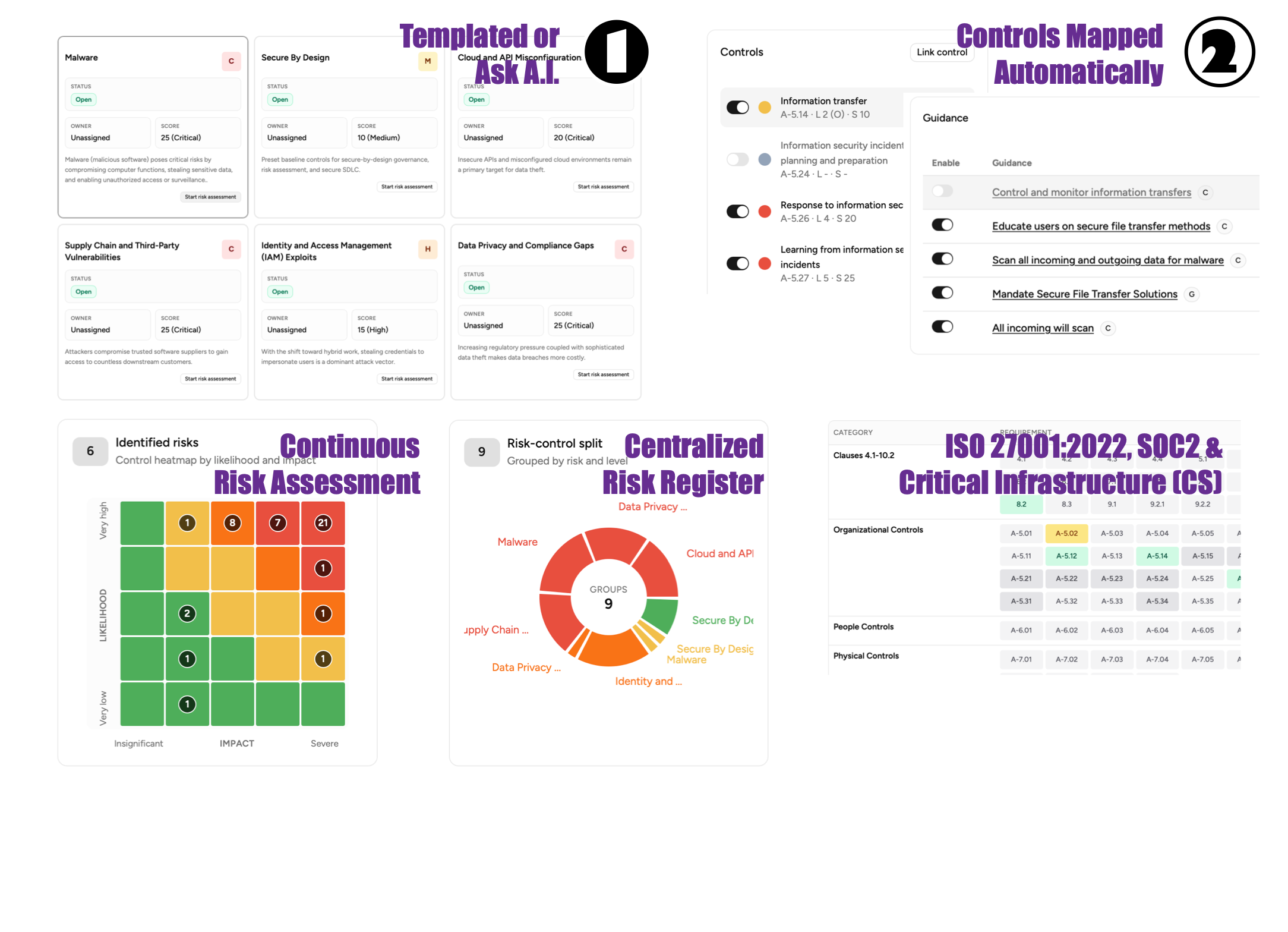
Templated Risks or Ask AI
To save time, reduce human error, improve analysis accuracy, facilitate better decision-making, and allows for quick, scalable assessments.
Rapid Identification & Assessment
AI algorithms analyze vast, complex datasets much faster than humans, identifying patterns and anomalies that might be missed, reducing human error and bias. AI systems provide continuous, 24/7 monitoring, offering immediate notifications when risk thresholds are crossed.
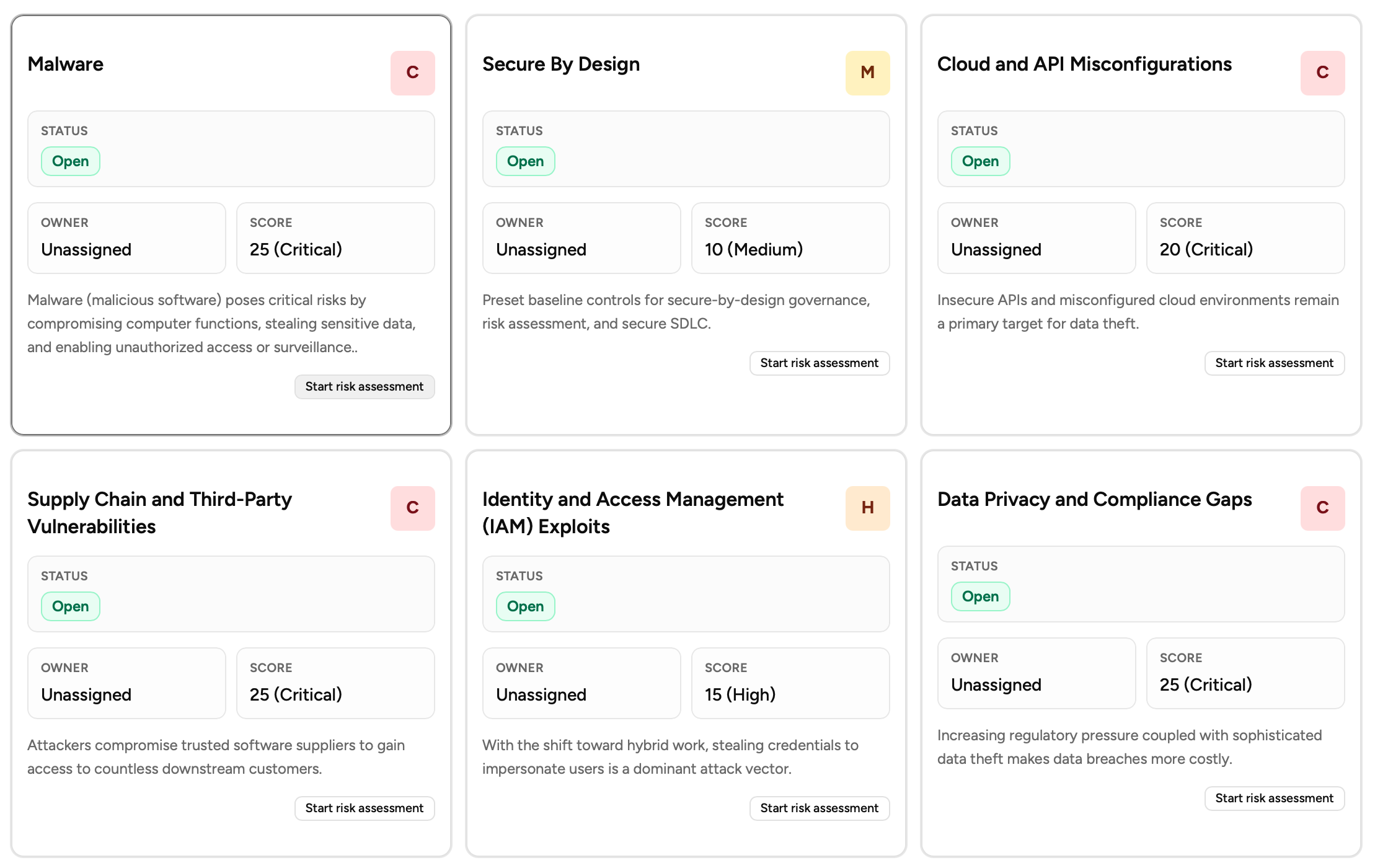
Centralized Risk Register
-
Consolidates risks from all departments into one repository, providing a complete view of organizational exposure, crucial for large organizations.
-
Reduces the risk of security gaps that occur when departments use separate systems, making communication more effective.
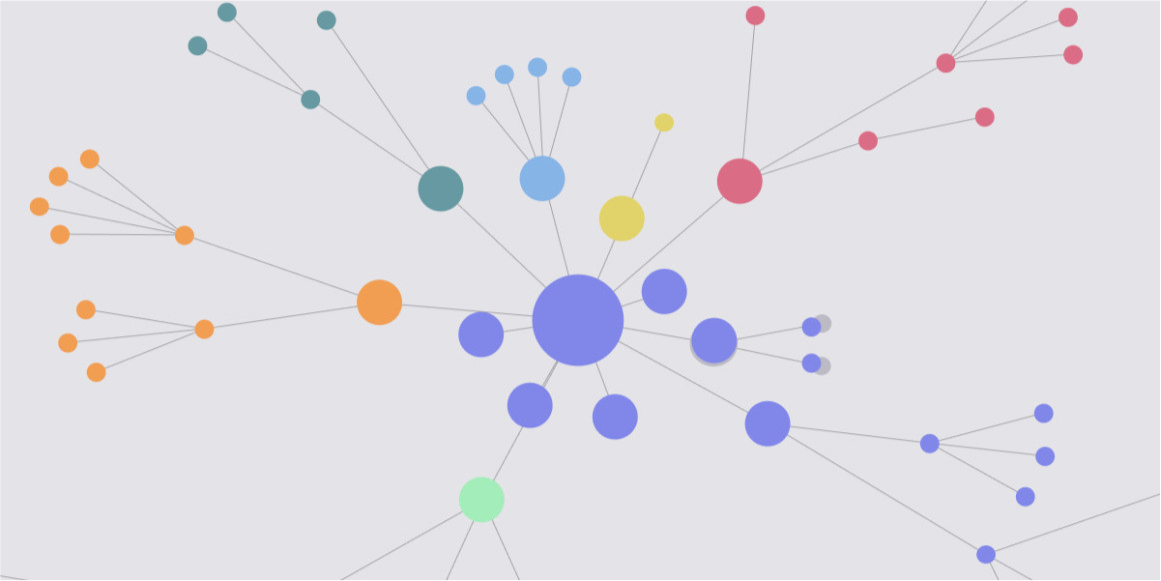
COMPLIANCE AUTOMATION
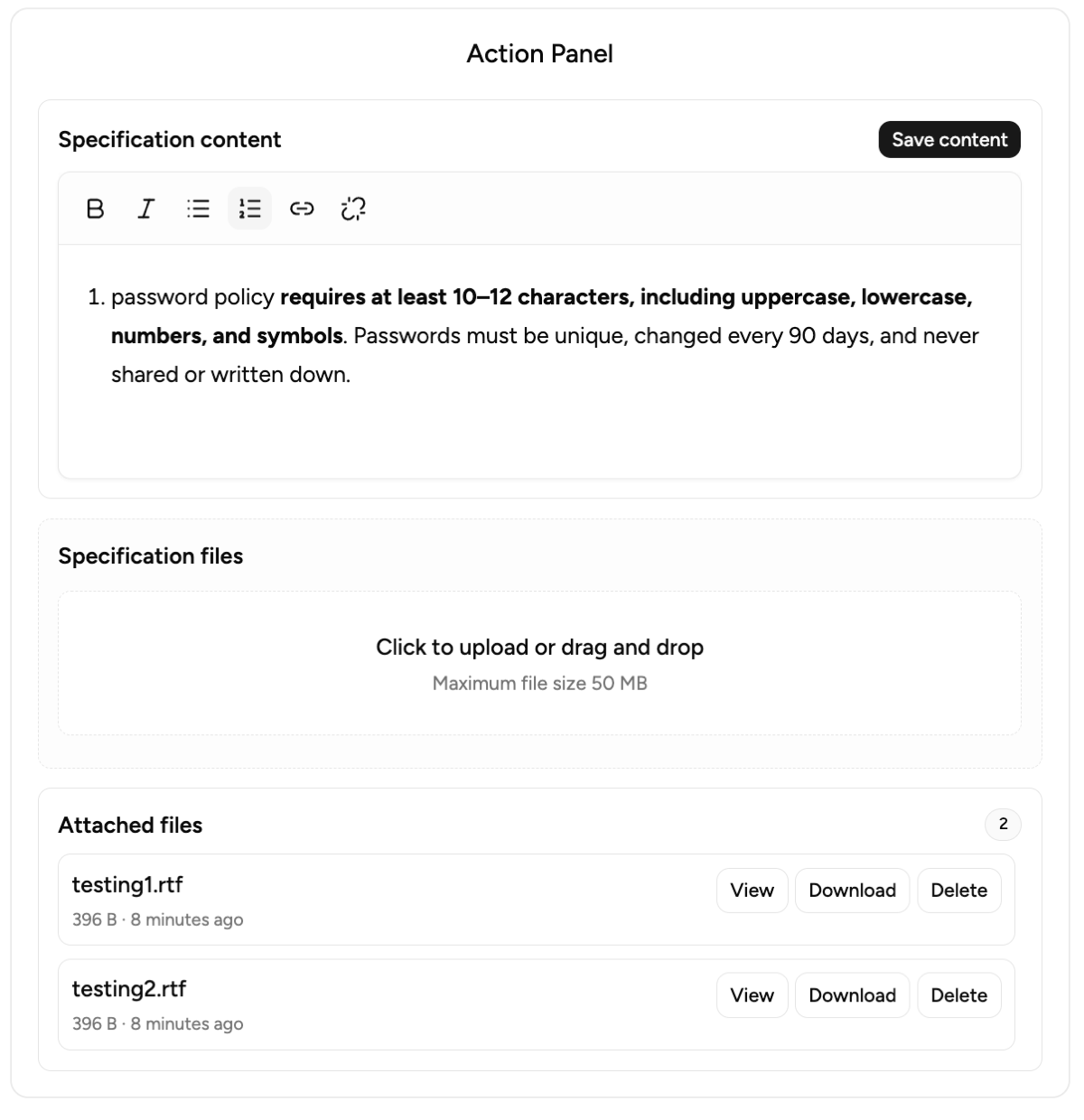
Complex Documentation
Managing 100+ policies, guidelines & procedures manually is overwhelming and error prone.Our Solution - Auditor-grade, customizable policy templates mapped to ISO27001 and other requirements
Resource Intensive
Traditional certification requires dedicated compliance teams and months of preparation.Our Solution - Streamlined workflows reduce certification time significantly with minimal team involvement.
Audit Preparation Stress
Manual evidence collection and organizing documentation for audits is overwhelming.Our Solution - Evidence collection mapped to applicable controls-guidance for audit-ready documentation.
Multiple Framework Compliance Burden
Navigating multiple frameworks alongside ISO27001 creates compliance burdens.Our Solution - AI-powered automated mappings across multiple framework simplified certification & re-certification.
Automated Mapping
AI Driven Insight

Risk Identification & Monitoring
Proactively detect risks by processing vast datasets, including unstructured data, far beyond human capacity.

Controls Based Risk Analysis
Transforms theoretical threats into actionable, measurable, and manageable operational realities.
Mapping Across Frameworks
Always use TLS encryption, don’t include sensitive information in URLs, rate limiting and safe error responses, etc.
Manual vs AI Driven
Results of little use
-
Flexibility: Rigid; requires manual updates to risk models periodically.
-
Data Sources: Historical, point-in-time, structured, and often limited.
-
Processing Speed: Slow, manual, and periodic (e.g., annually).
-
Accuracy: Prone to human fatigue, bias, and missing subtle patterns.
-
Good For: Superior for complex ethical judgment, regulatory clarity, and contextual nuance.
More accurate results
-
Flexibility: Adaptive; continuously learns and adjusts to new data.
-
Data Sources: Real-time, diverse & massive datasets, structured, and unstructured.
-
Processing Speed: Automated, near-instant, and continuous.
-
Accuracy: High precision; excels at complex, non-linear patterns.
-
Good For: unparalleled speed, pattern recognition and threats prediction.
Integrated IT Asset Register
From Spreadsheet to Centralized Visibility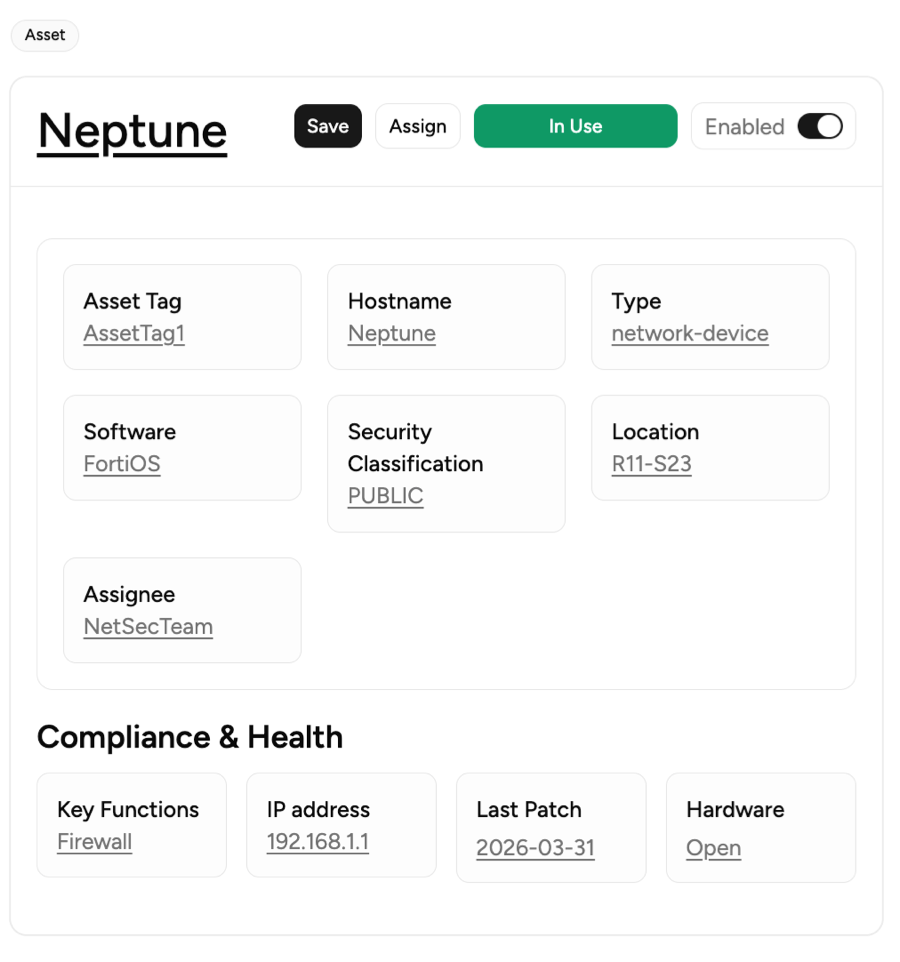
Improved Risk Identification
Provides visibility into all IT assets, allowing organizations to identify vulnerabilities, prioritize risks based on business impact, and implement proactive mitigation strategies. It also supports compliance and governance by maintaining accurate records of asset ownership, configuration, and status.
Prioritizing Risk Based on Business Criticality
-
Rules are generated automatically, no need to code bit-by-bit.
-
Dynamic rulerResponses generated automatically, no need to build one-by-one.
-
With variables, stateful rules are generated automatically.
-
Testing different scenarios, including error handling, edge cases, and performance testing.
Audit Ready Evidence
A centralized repository of current, timestamped, and comprehensive documentation proving security controls are active, not just planned.
Continuous Evidence
Not just a snapshot, but logs proving controls work over time, with timestamped records.
Why We are Better

Pricing - SaaS (Cloud Based)
Starter
Risk Automation (Templated or Ask AI)
HK$7,800/yearFor Startups
Max# Cybersecurity risks: 10
Max# User: 1
Max# Project: 1
Risk Assessment workflow
Controls & Guidance generated
Risk Register on-demand
Max Online Storage: 100 MB
Professional
Risk Automation & Compliance Automation
Contact UsFor Small Teams
Starter + Compliance Automation:
Max# Cybersecurity risks: 30
Max# User: 3
Max# Project: 3
Map to ISO27001:2022
Specification & Evidence
Max Online Storage: 1 GB
Enterprise
Risk Automation & Compliance Automation
CustomizableFor Enterprise
Professional + Integration:
# Cybersecurity risks: Unlimited
# User: Unlimited
# Project: Unlimited
Map to Multiple Frameworks
New / Changed Risks
Integration: JIRA
Accepted Payment Methods
Money Back Guarantee
If it’s not a perfect fit, receive a refund for un-used number of days.
SSL Encrypted Payment
Your information is protected by 256-bit SSL encryption.
The above prices do not include applicable taxes based on your billing address. The final price will be displayed on the checkout page, before the payment is completed
Got Questions? Look Here
What is automated risk assessment?
Automated risk assessment is the use of software and artificial intelligence to detect, analyze, and report risks with minimal manual input. Automated systems process huge data sets much faster than humans, producing risk scores and suggested actions in near real-time.
Does automation eliminate the need for human involvement?
Not at all. Automation handles repetitive tasks and number crunching, but decision-making and oversight are still essential. People review outputs, investigate flagged risks, and make final calls on actions.
Is automated risk assessment only for large enterprises?
No. Advances in cloud-based solutions and integrations mean organizations of any size can access automated risk assessment tools. Startups and small teams benefit just as much from saving time and reducing errors.
How often do automated assessments update risk scores?
Modern platforms can update risk scores continuously, reflecting changes as soon as new data appears. This enables a speedy response to threats that can arise at any time.
How do automated tools handle sensitive or confidential data?
RISK.HK solutions employ encryption, role-based access, and compliance with privacy frameworks like GDPR or HIPAA. Always review a provider’s data security credentials before deploying any tool.
Can I change plans or cancel at any time?
Yep. When you upgrade or downgrade your account, all charges are automatically pro-rated. That means if you need to, you can cancel any time.
Can I sign in without Multi-Factor Authentication?
For SaaS version, no. All user accounts are protected by Multi-Factor Authentication (Smartphone based Authenticator) after 30 days upon first successful sign-in.
Can automation miss potential risks?
Automated systems rely on strong data quality and accurate setup. Poor data input or badly configured rules can result in missed risks. Human review remains critical for unusual or emerging threats that algorithms aren’t trained to spot.

